Essential Cybersecurity Measures for Financial Services
Chosen theme: Essential Cybersecurity Measures for Financial Services. Safeguarding money is ultimately about safeguarding trust. Join us as we explore practical, human-centered defenses that keep customer data, payments, and reputation secure. Subscribe for weekly insights and share your experiences to help peers navigate today’s evolving threats.
Understanding Today’s Threat Landscape in Financial Services
Phishing, Social Engineering, and Business Email Compromise
Attackers weaponize urgency and familiarity to trick staff into transferring funds or resetting credentials. A mid-sized brokerage avoided a costly wire fraud when a teller questioned an urgent request and followed verification steps. Share your frontline stories and help others learn smarter, safer habits.
Ransomware and Double Extortion Tactics
Modern crews not only encrypt data but threaten to leak sensitive files to pressure payment. One community bank reduced impact by isolating critical systems and practicing restore drills. Tell us how your team tests backups and plans for worst-case scenarios to keep operations resilient.
Third-Party and Supply Chain Vulnerabilities
Outsourced services can introduce hidden exposure through APIs, shared credentials, or weak vendor controls. A credit union discovered risky S3 permissions during a routine review and tightened vendor access policies. Comment with your vendor vetting tips and help others strengthen their extended ecosystem.
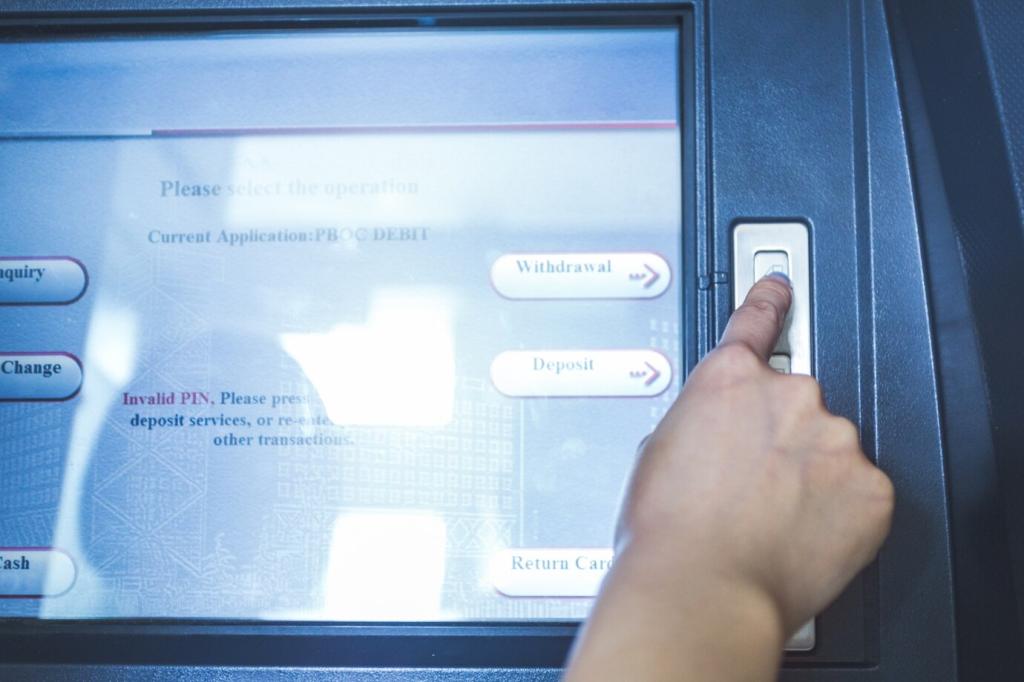
Zero Trust as a Foundation for Financial Security
Multi-factor authentication, conditional access, and privileged access management stop many credential attacks cold. A wealth firm cut account takeover attempts drastically by enforcing phishing-resistant MFA. Share how you balance user experience and security without slowing down relationship managers.
Zero Trust as a Foundation for Financial Security
Segment networks, restrict service accounts, and scope access to the minimum required. After microsegmenting trading systems, one firm observed fewer high-severity alerts. How do you prioritize initial segmentation boundaries without overwhelming your teams? Post your roadmap to inspire others.



Encryption at Rest and In Transit with Solid Key Management
Use strong ciphers, enforce TLS everywhere, and centralize keys in hardware security modules. A regional bank rotated keys automatically and reduced audit findings. What cadence and tooling keep your keys safe without creating operational friction? Share your proven practices below.
Tokenization and Minimization to Shrink Risk
Replace card numbers and personal details with tokens to reduce exposure and scope. A payments processor simplified compliance by tokenizing early in the flow. Comment with your strategy for balancing tokenization, usability, and analytics across reporting needs.
Data Loss Prevention and Cloud Guardrails
DLP policies, context-aware access, and storage lifecycle rules catch leaks before they go public. A lender prevented misdirected emails by scanning for account identifiers. Which cloud guardrails protect you most—predefined templates or custom policies? Add your lessons learned.
Framework Mapping and Control Ownership
Tie controls to GLBA, PCI DSS, and data protection laws while assigning accountable owners. One bank unified evidence across audits to speed attestations. How do you prevent duplicate efforts between teams? Share your governance playbook that keeps everyone aligned.
Risk Assessments, Metrics, and Board Reporting
Use quantified risk, meaningful KPIs, and trend lines to inform investment decisions. A board embraced MFA expansion after seeing reduced fraud metrics. What metrics best translate cyber risk into business language at your institution? Let us know to help peers communicate impact.
Incident Response and Notification Readiness
Practice playbooks, coordinate with legal, and prepare notifications within tight timelines often around 72 hours depending on jurisdiction. A brokerage used tabletop drills to streamline decisions. Do you include regulators in simulations? Share how you build confidence before real crises.
Automate SAST, DAST, and software composition analysis to catch flaws early. A savings app avoided a breach by flagging a vulnerable library in CI. What tools integrate smoothly with developer workflows? Share your favorites so teams can adopt them without friction.

Human Layer Security: Culture, Training, and Care
Make training scenario-based, brief, and frequent, aligned to real roles. A teller spotted an impersonation attempt after seeing a similar case in microlearning. What topics resonate with your teams most? Suggest them so we can craft practical content together.

Detection, Response, and Smart Automation
Tune policies to your environment, focusing on behaviors like credential dumping and lateral movement. A fraud team caught unusual processes within minutes. What detections earn top priority in your stack? Share use cases that deliver real value without alert fatigue.
Detection, Response, and Smart Automation
Great SIEM starts with clean, enriched telemetry mapped to clear hypotheses. A bank halved false positives by refining parsers and baselines. Which use cases do you recommend for quick wins? Comment to help peers build momentum in the first ninety days.
Resilience, Recovery, and Business Continuity
Backups, Immutability, and Recovery Objectives
Define RTO and RPO, store backups offline or immutable, and test restore speed realistically. A bank restored core services in hours after a drill. How often do you rotate recovery tests across teams? Share schedules that actually prove readiness.


Tabletop Exercises and Chaos Engineering for Security
Introduce controlled failure to expose brittle assumptions, from DNS to identity providers. A lender uncovered a single point of failure and fixed it fast. Do you include third parties in exercises? Tell us how you coordinate complex, multi-stakeholder rehearsals.
Join our mailing list
